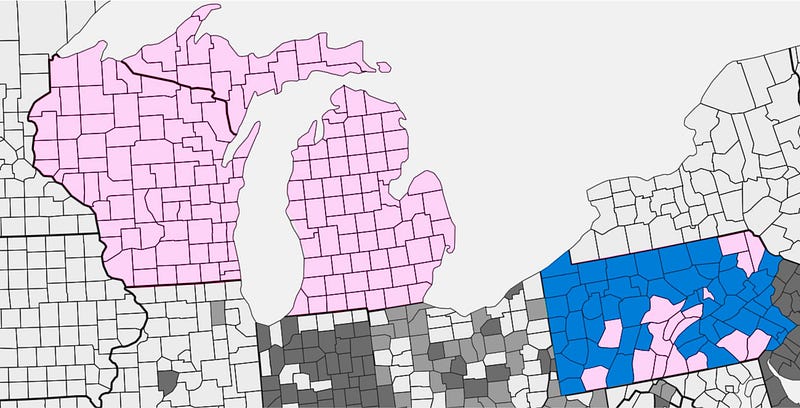
 “We the people” would simply like to take advantage of this opportunity while the Green Party presidential candidate Jill Stein is asserting her right as a presidential candidate to procedurally request a vote recount/ audit in the states of Wisconsin, Pennsylvania and Michigan, in order to uncover any and all vulnerabilities to our voting systems. For example, voting machines can now be forensically evaluated for possible manual tampering and computer experts can also check for hacking attempts on computerized voting machines.
“We the people” would simply like to take advantage of this opportunity while the Green Party presidential candidate Jill Stein is asserting her right as a presidential candidate to procedurally request a vote recount/ audit in the states of Wisconsin, Pennsylvania and Michigan, in order to uncover any and all vulnerabilities to our voting systems. For example, voting machines can now be forensically evaluated for possible manual tampering and computer experts can also check for hacking attempts on computerized voting machines.
“We the people” as stated in our U.S. constitution want the facts with complete transparency, as to how susceptible our vote is to being altered and what is being done to protect our rights to having an easy and secure access to the ballot box with the reassurance that any ballots cast will go to the voters’ intended candidates.
This is our chance to gather this data. The expert, Professor J. Alex Halderman who is pushing for these vote recounts/ audits has published in Medium.com, a 11/23/16 blog on this issue and here are some excerpts:
Want to Know if the Election was Hacked? Look at the Ballots
“You may have read at NY Mag that I’ve been in discussions with the Clinton campaign about whether it might wish to seek recounts in critical states. That article, which includes somebody else’s description of my views, incorrectly describes the reasons manually checking ballots is an essential security safeguard (and includes some incorrect numbers, to boot). Let me set the record straight about what I and other leading election security experts have actually been saying to the campaign and everyone else who’s willing to listen.”

“How might a foreign government hack America’s voting machines to change the outcome of a presidential election? Here’s one possible scenario. First, the attackers would probe election offices well in advance in order to find ways to break into their computers. Closer to the election, when it was clear from polling data which states would have close electoral margins, the attackers might spread malware into voting machines in some of these states, rigging the machines to shift a few percent of the vote to favor their desired candidate. This malware would likely be designed to remain inactive during pre-election tests, do its dirty business during the election, then erase itself when the polls close. A skilled attacker’s work might leave no visible signs — though the country might be surprised when results in several close states were off from pre-election polls.”
“Could anyone be brazen enough to try such an attack? A few years ago, I might have said that sounds like science fiction, but 2016 has seen unprecedented cyber- attacks aimed at interfering with the election. This summer, attackers broke into the email system of the Democratic National Committee and, separately, into the email account of John Podesta, Hillary Clinton’s campaign chairman, and leaked private messages. Attackers infiltrated the voter registration systems of two states Illinois and Arizona, and stole voter data. And there’s evidence that hackers attempted to breach election offices in several other states.”
“In all these cases, Federal agencies publicly asserted that senior officials in the Russian government commissioned these attacks. Russia has sophisticated cyber-offensive capabilities, and has shown a willingness to use them to hack elections. In 2014, during the presidential election in Ukraine, attackers linked to Russia sabotaged the country’s vote-counting infrastructure and, according to published reports, Ukrainian officials succeeded only at the last minute in defusing vote-stealing malware that was primed to cause the wrong winner to be announced. Russia is not the only country with the ability to pull off such an attack on American systems — most of the world’s military powers now have sophisticated cyber warfare capabilities.”.jpg)
“Were this year’s deviations from pre-election polls the results of a cyber- attack? Probably not. I believe the most likely explanation is that the polls were systematically wrong, rather than that the election was hacked. But I don’t believe that either one of these seemingly unlikely explanations is overwhelmingly more likely than the other. The only way to know whether a cyber- attack changed the result is to closely examine the available physical evidence — paper ballots and voting equipment in critical states like Wisconsin, Michigan, and Pennsylvania. Unfortunately, nobody is ever going to examine that evidence unless candidates in those states act now, in the next several days, to petition for recounts.”
What’s to stop an attack like this from succeeding?
“America’s voting machines have serious cyber- security problems. That isn’t news. It’s been documented beyond any doubt over the last decade innumerous peer-reviewed papers and state-sponsored studies by me and by other computer security experts. We’ve been pointing out for years that voting machines are computers, and they have reprogrammable software, so if attackers can modify that software by infecting the machines with malware, they can cause the machines to give any answer whatsoever. I’ve demonstrated this in the laboratory with real voting machines- in just a few seconds, anyone can install vote-stealing malware on those machines that silently alters the electronic records of every vote.”
“It doesn’t matter whether the voting machines are connected to the Internet. Shortly before each election, poll workers copy the ballot design from a regular desktop computer in a government office, and use removable media (like the memory card from a digital camera) to load the ballot onto each machine. That initial computer is almost certainly not well secured, and if an attacker infects it, vote-stealing malware can hitch a ride to every voting machine in the area. There’s no question that this is possible for technically sophisticated attackers. (If my Ph.D. students and I were criminals, I’m sure we could pull it off.) If anyone reasonably skilled is sufficiently motivated and willing to face the risk of getting caught, it’s happened already.”
“Why hasn’t more been done about this? In the U.S., each state (and often individual counties or municipalities.) selects its own election technology, and some states have taken steps to guard against these problems. (For instance, California banned the use of the most dangerous computer voting machines in 2007 as a result of vulnerabilities that I and other computer scientists found.) But many states continue to use machines that are known to be insecure — sometimes with software that is a decade or more out of date — because they simply don’t have the money to replace those machines.”
Link to the Complete Text:Want to Know if the Election was Hacked? Look at the Ballots – Medium…11/23/16